Glossary of Acronyms
. Systems & Hardware (The “Tech”)
These are the physical and digital components that keep an industrial facility running.
- BAS – Breach and Attack Simulation
- CPS – Cyber-Physical Systems
- DCOM – Communication Port (Distributed Component Object Model)
- DCS – Direct Control System
- DCS (v2) – Distributed Control Systems
- HMI – Human Machine Interface
- HVAC – Heating, Ventilation, and Air Conditioning
- ICS – Industrial Control Systems
- MES – Manufacturing Execution System
- OT – Operations Technology
- PLC – Programmable Logic Controller
- SCADA – Supervisory Control and Data Acquisition
- TI – Threat Intelligence
2. Risk & Analysis Frameworks
These are the methodologies used to identify vulnerabilities and prioritize what to fix first.
ZCR – Zone and Conduit Requirement (Defining security boundaries as per IEC 62443)
CJA – Crown Jewel Analysis (Identifying the most critical assets in a network)
HSSE Risks – Health, Safety, Security, and Environmental Risks (The four primary areas of impact in industrial incidents)
SuC – System under Consideration (The specific scope of a security assessment)
ZCR – Zone and Conduit Requirement (Defining security boundaries as per IEC 62443)
3. Security Strategy & Compliance
The “rules of the road” and the tools used to defend the network.
- AIC – Availability, Integrity, and Confidentiality (The “CIA” triad, often prioritized as A-I-C in industrial settings)
- CISA – US Cybersecurity & Infrastructure Security Agency
- EDR Tool – Endpoint Detection and Response Tool (Software that monitors end-user devices to detect and respond to cyber threats)
- IRP – Incident Response Plan
- NIS (listed as NIST) – Network and Information Systems Directive
- NIS2 (listed as NIST-2) – Network and Information Systems Directive-2
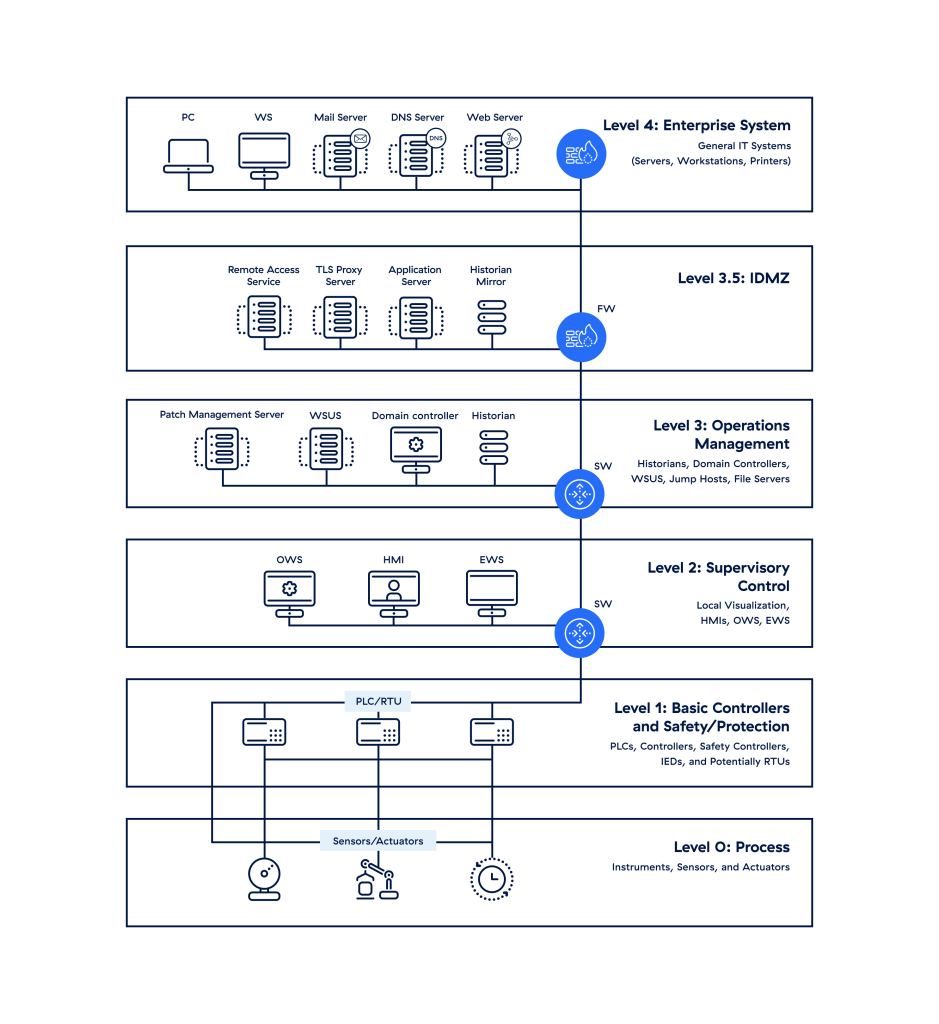
Purdue Model
Courtesy of Zscaler: https://www.zscaler.com/resources/security-terms-glossary/what-is-purdue-model-ics-security
ISA/IEC-62443 Framework
Original Source: https://www.fortinet.com/uk/resources/cyberglossary/iec-62443
Foundational requirements of IEC 62443 compliance
Each IEC 62443 security level is associated with seven foundational requirements to ensure significant security. These are 7 foundational requirements:
- FR1: Identification and Authentication Control: Every user, including humans, software processes, devices and other entities, should be identified and authenticated before accessing the ICS system.
- FR2: Use Control: Every authenticated user should be granted assigned privileges to perform requested actions on the system.
- FR3: System Integrity: System’s integrity is maintained by protecting it from unauthorized users and changes.
- FR4: Data Confidentiality: Sensitive & confidential information is protected from unauthorized access.
- FR5: Restricted Data Flow: Control system is prevented from data flow/leakage in various zones through segmentation.
- FR6: Timely Response to Events: Prompt response to security incidents and appropriate actions are taken.
- FR7: Resource Availability: Essential resources are maintained and remain available during an attack to avoid degradation of services.
IEC 62443 Security Levels (SL)
The IEC 62443 framework includes a series of security levels(SL) designed to address cybersecurity risks in industrial automation and control systems. There are four security levels:
Security Levels:
SL 4: Protects against intentional violation using advanced means with extended resources. This level shields from advanced threats that could have a destructive impact.
SL 1: Protects against casual or coincidental violation. This level guards from unintentional, and non-malicious human errors.
SL 2: Protects against intentional violation using simple means. This level defends against threats posed by individuals with low motivation, resources, basic tools and techniques.
SL 3: Protects against intentional violation using sophisticated means. This level saves from attacks by individuals with moderate resources, and motivated adversaries using advanced tools.
How does IEC 62443 mitigate threats?
IEC 62443 mitigates cyberattacks through a structured framework that includes,
- Layered Security Approach
- Network Segmentation
- Risk Assessment
- Defining Zones and Conduits
- Regular Reviews
- Leveraging Advanced Technologies
IEC 62443 strengthens resilience against evolving cyber threats by addressing vulnerabilities throughout the system lifecycle and encouraging collaboration among stakeholders.
Benefits of adopting IEC 62443 for industrial cybersecurity
Enhanced security levels for industrial automation systems
Operational resilience
Regulatory compliance